AES is short for Advanced Encryption Standard. It's a symmetric block cipher used by the American government to encrypt sensitive data. AES is also used by individuals and corporations alike to lock away classified or otherwise valuable information.
- Aes-256-cbc Key Iv
- Aes 256 Cbc Key Bank
- Openssl Aes-256-cbc Key
- Aes 256 Cbc Key Code
- Aes 256 Cbc Key Change
AES was created by the National Institute of Standards and Technology (NIST) and became an effective federal government standard in 2002, after being in development for five years. Development of AES began in 1997 when it became clear its predecessor, the Data Encryption Standard (DES), was no longer cut out for the job. Hackers had begun to brute force their way through DES' encryption algorithms and the American government called for a new, more sophisticated encryption tool, which could do the job in the 21st century.
AES was meant to be streamlined and easy to in both software and hardware along with other more restricted environments.
Laravel encryption method with using AES-256-CBC and base64 key for Swift. Swift ios laravel encryption aes-256-cbc Updated Aug 7, 2017; Swift; ash-shell. The AES stands for Advanced Encryption Standard. This project is started in 1997 by The National Institute of Standards and Technology ( NIST ) as an alternative for Data Encryption Standard ( DES ). This symmetric/reversible key encryption block clipper is equipped to handle 128-bit blocks, using keys sized at 128, 192, and 256 bits.
One of the boons AES' designers received was the transparency of the selection process itself. The design of the new work process was open to the public, which allowed the NIST to receive constructive criticism from all manner of sources.

Aes-256-cbc Key Iv
The National Institute of Standards and Technology requested that the new encryption standard algorithm be a block cipher capable of dealing with 128-bit blocks and must use 128, 192, and 256 bit-sized keys. The institute had other requirements such as:
Security
The most vital criterion. AES was judged in comparison with other encryption algorithms. While other factors were considered, its security rating was the most important component.
Cost
- Give our aes-256-cbc encrypt/decrypt tool a try! Aes-256-cbc encrypt or aes-256-cbc decrypt any string with just one mouse click.
- In this articles I’m gonna show you how to Encryt and Decrypt data by Languages that I mentioned above, So let’s start with shell script. Echo -n 'ball' openssl aes-256-cbc -a -nosalt -K.
- Imports System.IO Imports System.Security.Cryptography Class AesExample Public Shared Sub Main Dim original As String = 'Here is some data to encrypt!' ' Create a new instance of the Aes ' class. This generates a new key and initialization ' vector (IV). Using myAes As Aes = Aes.Create ' Encrypt the string to an array of bytes.
AES was intended to be released without any cost, royalties or profit. Instead, the candidate algorithms were judged on their memory and resource consumption.
Implementation
Another important factor was the candidates' ease of use and implementation into various hardware and software configurations. NIST wanted an algorithm that was as streamlined as possible.
Choosing AES algorithms
Fifteen competing symmetric key algorithm designs were subjected to preliminary analysis by the world cryptographic community, including the National Security Agency (NSA). In August 1999, NIST selected five algorithms for more extensive analysis.
After extensive testing, the National Institute of Standards chose the Rijndael cipher (named after its Belgian creators, whose last names are Daemen and Rijmen). Rijndael was chosen as the algorithm for AES in October 2000 and published by NIST as U.S. FIPS PUB 197. Rijndael became a federal standard in 2002.
Later, in 2003, the American federal government declared that AES could be put in use to protect top secret data, which led to the Advanced Encryption Standard becoming the default algorithm for encrypting classified info, and also the first encryption algorithm approved by the NSA made open for the general public.
AES was extremely successful in its work of guarding U.S. state secrets. This lead to its widespread exploitation in the private security sector, which lead to AES becoming the most used encryption algorithm in symmetric key cryptography.
How AES encryption functions
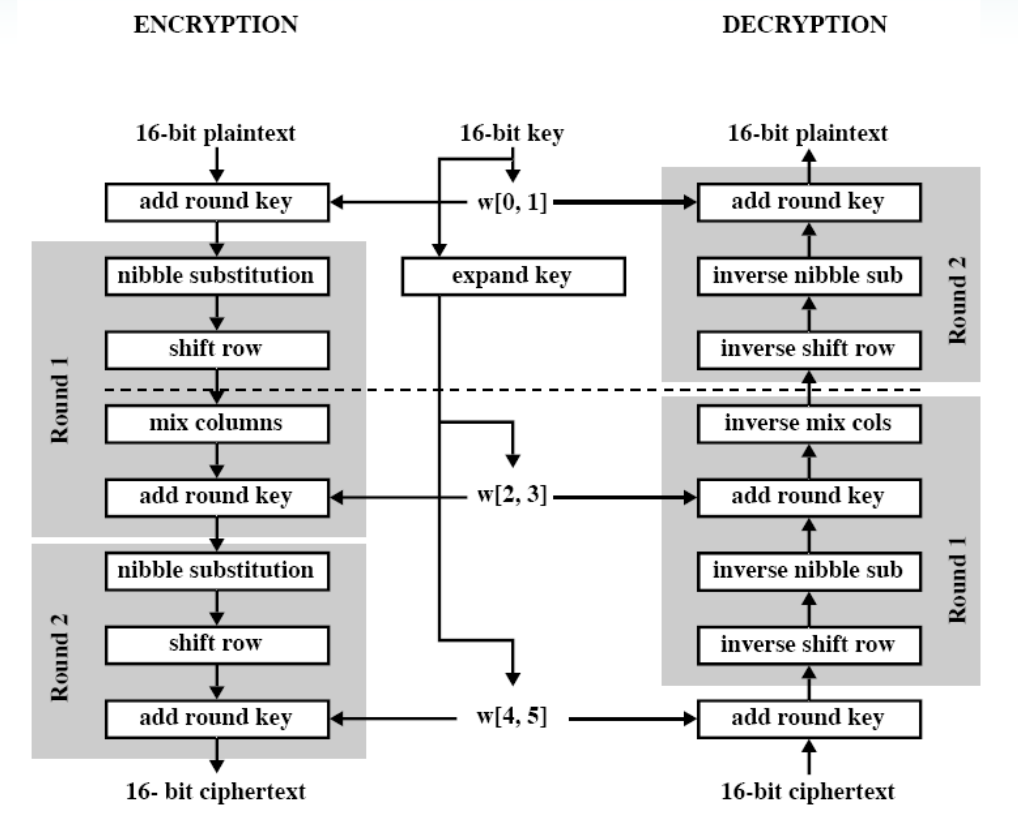
Advanced Encryption Standard is built from three block ciphers: AES-128, AES-192, and AES-256. Each of these encrypts and decrypts data in chunks of 128 bits by using cryptographic keys of 128-, 192- or 256-bits.The cipher was designed to accept additional block sizes and key lengths, but those functions were dropped when Rijndael became AES. All symmetric encryption ciphers use the same key for encrypting and decrypting data, which means the sender and the receiver must both have the same key. Every key length is viewed as adequate to protect classified data up to the 'Secret' level with 'Top Secret' info needing either 192-bit or 256-bit key lengths. 128-bit keys have 10 rounds, 192-bit keys have 12, and finally 14 rounds for 256-bit keys. What are rounds? They correspond to multiple processing steps, which include permutation and substitution of the encrypted text, which transforms it into its encrypted form.
The first step in the AES encryption process is substituting the information using a substitution table; the second transmutation changes data rows and the third shifts columns. The last transformation is a basic exclusive XOR process done on each column using a different part of the encryption key. The longer the encryption key, the more rounds are needed.

Applies to: SQL Server (all supported versions) Azure SQL Database Azure SQL Managed Instance
This document describes encryption algorithms and mechanisms to derive cryptographic material used in the Always Encrypted feature in SQL Server and Azure SQL Database.
Keys, key stores, and key encryption algorithms
Always Encrypted uses two types of keys: Column master keys and column encryption keys.
A column master key (CMK) is a key encrypting key (for example, a key that is used to encrypt other keys) that is always in a client's control, and is stored in an external key store. An Always Encrypted-enabled client driver interacts with the key store via a CMK store provider, which can be either part of the driver library (a Microsoft/system provider) or part of the client application (a custom provider). Client driver libraries currently include Microsoft key store providers for Windows Certificate Store and hardware security modules (HSMs). For the current list of providers, see CREATE COLUMN MASTER KEY (Transact-SQL). An application developer can supply a custom provider for an arbitrary store.
A column encryption key (CEK), is a content encryption key (for example, a key that is used to protect data) that is protected by a CMK.
All Microsoft CMK store providers encrypt CEKs by using RSA with Optimal Asymmetric Encryption Padding (RSA-OAEP). The key store provider that supports Microsoft Cryptography API: Next Generation (CNG) in .NET Framework (SqlColumnEncryptionCngProvider Class) uses the default parameters specified by RFC 8017 in Section A.2.1. Those default parameters are using a hash function of SHA-1 and a mask generation function of MGF1 with SHA-1. All other key store providers use SHA-256.
Always Encrypted internally uses FIPS 140-2 validated cryptographic modules.
Data Encryption Algorithm
Always Encrypted uses the AEAD_AES_256_CBC_HMAC_SHA_256 algorithm to encrypt data in the database.
AEAD_AES_256_CBC_HMAC_SHA_256 is derived from the specification draft at https://tools.ietf.org/html/draft-mcgrew-aead-aes-cbc-hmac-sha2-05. It uses an Authenticated Encryption scheme with Associated Data, following an Encrypt-then-MAC approach. That is, the plaintext is first encrypted, and the MAC is produced based on the resulting ciphertext.
In order to conceal patterns, AEAD_AES_256_CBC_HMAC_SHA_256 uses the Cipher Block Chaining (CBC) mode of operation, where an initial value is fed into the system named the initialization vector (IV). The full description of the CBC mode can be found at https://csrc.nist.gov/publications/nistpubs/800-38a/sp800-38a.pdf.
AEAD_AES_256_CBC_HMAC_SHA_256 computes a ciphertext value for a given plaintext value using the following steps.
Step 1: Generating the initialization vector (IV)
Always Encrypted supports two variations of AEAD_AES_256_CBC_HMAC_SHA_256:
Randomized
Deterministic
For randomized encryption, the IV is randomly generated. As a result, each time the same plaintext is encrypted, a different ciphertext is generated, which prevents any information disclosure.
If there's deterministic encryption, the IV isn't randomly generated, but instead it's derived from the plaintext value using the following algorithm:
Where iv_key is derived from the CEK in the following way:
The HMAC value truncation is performed to fit one block of data as needed for the IV.As a result, deterministic encryption always produces the same ciphertext for a given plaintext value, which enables inferring whether two plaintext values are equal by comparing their corresponding ciphertext values. This limited information disclosure allows the database system to support equality comparison on encrypted column values.
Aes 256 Cbc Key Bank
Deterministic encryption is more effective in concealing patterns, compared to alternatives, such as using a pre-defined IV value.
Openssl Aes-256-cbc Key
Step 2: Computing AES_256_CBC Ciphertext
After computing the IV, the AES_256_CBC ciphertext is generated:

Where the encryption key (enc_key) is derived from the CEK as follows.
Aes 256 Cbc Key Code
Step 3: Computing MAC
Subsequently, the MAC is computed using the following algorithm:
Where:
Step 4: Concatenation
Finally, the encrypted value is produced by concatenating the algorithm version byte, the MAC, the IV, and the AES_256_CBC ciphertext:
Ciphertext Length
The lengths (in bytes) of particular components of AEAD_AES_256_CBC_HMAC_SHA_256 ciphertext are:
versionbyte: 1
MAC: 32
IV: 16
aes_256_cbc_ciphertext:
(FLOOR (DATALENGTH(cell_data)/ block_size) + 1)* block_size, where:block_size is 16 bytes
cell_data is a plaintext value
Therefore, the minimal size of aes_256_cbc_ciphertext is 1 block, which is 16 bytes.
Thus, the length of ciphertext, resulting from encrypting a given plaintext values (cell_data), can be calculated using the following formula:
For example:
A 4-byte long int plaintext value becomes a 65-byte long binary value after encryption.
A 2,000-byte long nchar(1000) plaintext values becomes a 2,065-byte long binary value after encryption.
The following table contains a complete list of data types and the length of ciphertext for each type.
| Data Type | Ciphertext Length [bytes] |
|---|---|
| bigint | 65 |
| binary | Varies. Use the formula above. |
| bit | 65 |
| char | Varies. Use the formula above. |
| date | 65 |
| datetime | 65 |
| datetime2 | 65 |
| datetimeoffset | 65 |
| decimal | 81 |
| float | 65 |
| geography | N/A (not supported) |
| geometry | N/A (not supported) |
| hierarchyid | N/A (not supported) |
| image | N/A (not supported) |
| int | 65 |
| money | 65 |
| nchar | Varies. Use the formula above. |
| ntext | N/A (not supported) |
| numeric | 81 |
| nvarchar | Varies. Use the formula above. |
| real | 65 |
| smalldatetime | 65 |
| smallint | 65 |
| smallmoney | 65 |
| sql_variant | N/A (not supported) |
| sysname | N/A (not supported) |
| text | N/A (not supported) |
| time | 65 |
| timestamp (rowversion) | N/A (not supported) |
| tinyint | 65 |
| uniqueidentifier | 81 |
| varbinary | Varies. Use the formula above. |
| varchar | Varies. Use the formula above. |
| xml | N/A (not supported) |
.NET Reference
For details about the algorithms, discussed in this document, see the SqlAeadAes256CbcHmac256Algorithm.cs, SqlColumnEncryptionCertificateStoreProvider.cs, and SqlColumnEncryptionCertificateStoreProvider.cs files in the .NET Reference.