Dominator pro xss cracked. Auto Campaign Resume Algorithm, So no more worry if your Redditplus Dominator got closed while a process was running. Algorithm to Increase Only Unique Groups for Profiles In Same Campaign. View the revised XB1 Strike Pack FPS 2.0.2 Dominator Manual HERE. NOTE: We wanted to get this update out to everyone as soon as possible so you can enjoy the XB1 Strike Pack FPS Dominator to the fullest extent. Although the update is technically in BETA, we have spent exhaustive hours testing. StrikeMax Software Download – StrikeMax Software is Legacy software that is no longer supported. Please update your Strike Pack using the Universal Updater Found here for PC and for MAC. After updating, StrikeMax Software will no longer function. Use Mod Central for PC to configure your Strike Pack.
In the previous article of this series, we explained how to prevent from SQL-Injection attacks. In this article we will see a different kind of attack called XXS attacks.
XSS stands for Cross Site Scripting.
XSS is very similar to SQL-Injection. In SQL-Injection we exploited the vulnerability by injecting SQL Queries as user inputs. In XSS, we inject code (basically client side scripting) to the remote server.
Types of Cross Site Scripting
XSS attacks are broadly classified into 2 types:
- Non-Persistent
- Persistent
1. Non-Persistent XSS Attack
In case of Non-Persistent attack, it requires a user to visit the specially crafted link by the attacker. When the user visit the link, the crafted code will get executed by the user’s browser. Let us understand this attack better with an example.
Example for Non-Persistent XSS
Dominator Pro Xss Cracked Version
index.php: Vw navigation rns 310 cd download.
Dominator Pro Xss Cracked Screen
Example 1:
Now the attacker will craft an URL as follows and send it to the victim:
When the victim load the above URL into the browser, he will see an alert box which says ‘attacked’. Even though this example doesn’t do any damage, other than the annoying ‘attacked’ pop-up, you can see how an attacker can use this method to do several damaging things.
Example 2:
For example, the attacker can now try to change the “Target URL” of the link “Click to Download”. Instead of the link going to “xssattackexamples.com” website, he can redirect it to go “not-real-xssattackexamples.com” by crafting the URL as shown below:
In the above, we called the function to execute on “window.onload”. Because the website (i.e index.php) first echos the given name and then only it draws the <a> tag. So if we write directly like the one shown below, it will not work, because those statements will get executed before the <a> tag is echoed
Normally an attacker tends not to craft the URL which a human can directly read. So he will encode the ASCII characters to hex as follows.
which is same as:
Now the victim may not know what it is, because directly he cannot understand that the URL is crafted and their is a more chance that he can visit the URL.

2. Persistent XSS Attack
In case of persistent attack, the code injected by the attacker will be stored in a secondary storage device (mostly on a database). The damage caused by Persistent attack is more than the non-persistent attack. Here we will see how to hijack other user’s session by performing XSS.
Session
HTTP protocol is a stateless protocol, which means, it won’t maintain any state with regard to the request and response. All request and response are independent of each other. But most of the web application don’t need this. Once the user has authenticated himself, the web server should not ask the username/password for the next request from the user. To do this, they need to maintain some kind of states between the web-browser and web-server which is done through the “Sessions”.
When the user login for the first time, a session ID will be created by the web server and it will be sent to the web-browser as “cookie”. All the sub-sequent request to the web server, will be based on the “session id” in the cookie.
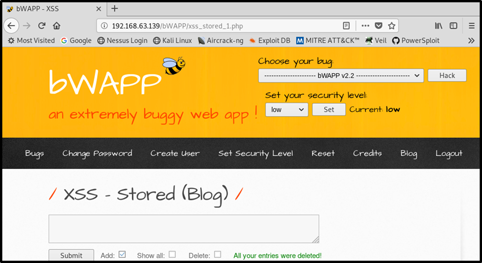
Examples for Persistent XSS Attack
This sample web application we’ve given below that demonstrates the persistent XSS attack does the following:
- There are two types of users: “Admin” and “Normal” user.
- When “Admin” log-in, he can see the list of usernames. When “Normal” users log-in, they can only update their display name.

login.php:
Dominator Pro Xss Cracked Door
home.php:
Now the attacker log-in as a normal user, and he will enter the following in the textbox as his display name:
Dominator Pro Xss Cracked Download
The above information entered by the attacker will be stored in the database (persistent).
Now, when the admin log-in to the system, he will see a link named “My Name” along with other usernames. When admin clicks the link, it will send the cookie which has the session ID, to the attacker’s site. Nakshatra table pdf. Now the attacker can post a request by using that session ID to the web server, and he can act like “Admin” until the session is expired. The cookie information will be something like the following:
Once the hacker knows the PHPSESSID, he can use this session to get the admin privilege until PHPSESSID expires.
How to download minecraft bedrock edition on mac. To understand this more, we can use a firefox addon called “Tamper Data”, which can be used to add a new HTTP header called “Cookies” and set the value to “PHPSESSID=vmcsjsgear6gsogpu7o2imr9f3”.
We’ll cover how to use “Tamper Data” in future article of this series.